Free Report
Veeam is a Four-Time Leader and Outperformer
See why Veeam’s Kubernetes data protection solution outranks competitors
- Kasten K10 Use Cases
- Disaster Recovery
Disaster Recovery
Kubernetes Native Disaster Recovery
- Return to operation after ransomware attacks
- Recover from malicious data loss
- Protect from unintentional failures
Securely Replicate Your Backups to Another Site
Automated DR workflows for Kubernetes
Kasten K10 delivers DR with robust scheduled and on-demand workflows.
Automatic Import and Restore in K8s Environments
Automatically import and restore changes to a cluster.
Maintain Multiple Restore-Ready Backups for Kubernetes
Maintain multi-component container applications from backups.
How Organizations View Disaster Recovery
Disaster Recovery Situations Are More Common Than You Think
Return to Operation After Ransomware Attacks
Kasten K10 is part of effective backup and encryption strategies that control offline and offsite data backups to preserve data sovereignty, even in the event of a network breach.
Recover From Unintentional Failures
Natural disasters such as unplanned power outages can be mitigated by implementing a Kasten K10 production-ready backup strategy.
Protect From Malicious Data Loss
When live information, backup, and in-transit data is encrypted by Kasten K10, the probability of a severe data loss and the ramifications of its liability are reduced.
Recover From Infrastructure or Hardware Failures
When IT is using Kasten K10 for data protection, Kubernetes applications and data are protected in the event of a disaster incident due to infrastructure or hardware failures.
Use Cases for Kasten K10
Customers Protected by Veeam










FAQs
How does Kasten K10 support disaster recovery in Kubernetes?
Can Kasten K10 help recover from ransomware and data breaches?
How does Kasten K10 ensure data security during DR?
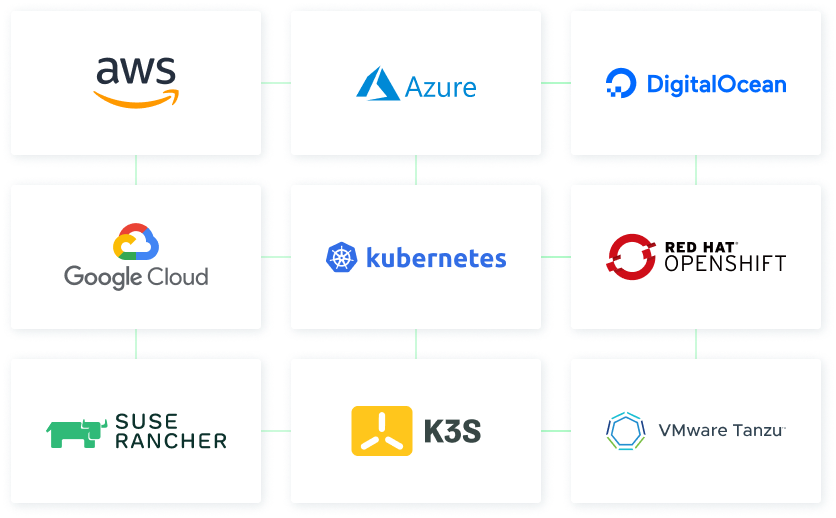
Does Kasten K10 offer cross-cloud DR flexibility?
Radical Resilience Starts Here
hybrid cloud and the confidence you need for long-term success.